A recent report from Microsoft Threat Intelligence has unveiled two distinct yet equally menacing cybersecurity campaigns actively targeting a diverse range of organizations, from critical infrastructure to educational institutions. One campaign involves a fast-moving ransomware operation orchestrated by a threat group identified as Storm-1175, which is deploying Medusa ransomware with unprecedented speed, often encrypting systems within 24 hours of initial compromise. Concurrently, a separate, sophisticated espionage campaign attributed to the Russian military intelligence-linked group Forest Blizzard (also known as APT28 or Fancy Bear) has compromised thousands of small office/home office (SOHO) routers, leveraging them for adversary-in-the-middle (AiTM) attacks to surreptitiously monitor victims’ network traffic and collect sensitive data. These twin threats underscore the persistent and evolving dangers faced by organizations globally, demanding heightened vigilance and robust defensive measures.
The Blistering Pace of Medusa Ransomware: Storm-1175’s High-Tempo Operations
Microsoft’s detailed analysis, published in an April 6 blog post, paints a grim picture of Storm-1175’s operational tempo. This threat group has distinguished itself through its rapid exploitation of recently disclosed vulnerabilities, swiftly moving from initial access to data exfiltration and ransomware deployment. Since 2023, Storm-1175 has been observed exploiting a staggering array of over 16 vulnerabilities, demonstrating a wide-ranging arsenal capable of breaching various internet-facing assets. These vulnerabilities have spanned critical infrastructure components, including Microsoft Exchange servers, and widely used file transfer applications such as GoAnywhere MFT and CrushFTP. The group’s ability to weaponize zero-day vulnerabilities a full week before their public disclosure in some instances highlights a sophisticated intelligence-gathering capability and a proactive approach to exploitation, granting them a significant head start over potential defenders.
The primary targets of Storm-1175’s Medusa ransomware campaign are predominantly concentrated in healthcare organizations, education institutions, professional services firms, and entities within the financial sector. These sectors are particularly attractive to ransomware operators due to the sensitive nature of their data, their often-stretched IT resources, and the critical need for operational continuity, which can increase the likelihood of ransom payment. Geographically, the attacks have been observed across the United States, Australia, and the United Kingdom, indicating a global reach and a strategic focus on economically significant regions.
The attack chain employed by Storm-1175 follows a well-established, albeit alarmingly efficient, pattern. Upon successful exploitation of a vulnerable web-facing system, the group prioritizes establishing persistence within the compromised network, often by creating new administrative accounts. This is quickly followed by the deployment of remote monitoring and management (RMM) tools, which facilitate lateral movement across the network. The group then proceeds to dump credentials, typically using tools like Mimikatz, to elevate privileges and gain access to more critical systems. A critical step before the final payload deployment involves tampering with or disabling security software to evade detection. Finally, Medusa ransomware is unleashed across the network using legitimate deployment tools, such as PDQ Deployer, to maximize the speed and breadth of encryption. This systematic approach, coupled with rapid execution, minimizes the window of opportunity for detection and response by victim organizations.
Microsoft’s investigation further revealed Storm-1175’s reliance on a blend of commodity tools and legitimate RMM platforms. Beyond Mimikatz for credential theft, the group has been seen leveraging platforms such as Atera, Level, N-able, and ConnectWise ScreenConnect. The use of legitimate tools complicates detection, as their activity can blend in with normal network operations. A key aspect of their strategy is the use of Rclone, a versatile command-line program, to exfiltrate data prior to encryption. This enables the group to employ double-extortion tactics, threatening to publish stolen sensitive information on Medusa’s dedicated leak site if the ransom is not paid, thereby increasing pressure on victims. The financial ramifications of such attacks are severe, with average ransom payments often running into hundreds of thousands or even millions of dollars, in addition to the immense costs associated with downtime, data recovery, and reputational damage.
The Silent Surveillance of Forest Blizzard: Router-Based Espionage
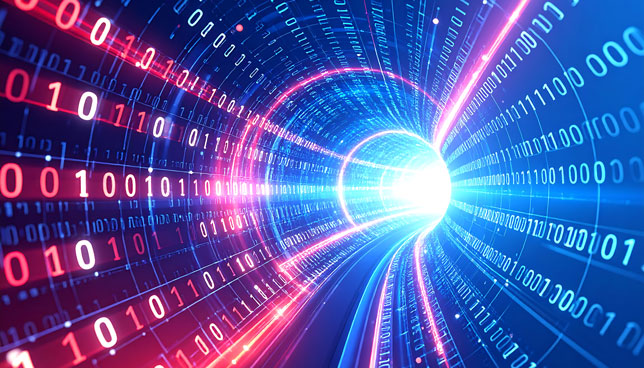
In parallel to the ransomware onslaught, Microsoft’s April 7 blog post shed light on a distinct but equally troubling threat: a sophisticated cyber espionage campaign conducted by Forest Blizzard. This group, widely recognized as APT28 or Fancy Bear and linked to Russia’s GRU military intelligence, has been actively compromising insecure SOHO routers since at least August 2025. The campaign’s modus operandi involves modifying the DNS settings of compromised routers, thereby redirecting victims’ network traffic through attacker-controlled infrastructure. This allows Forest Blizzard to conduct adversary-in-the-middle attacks, silently intercepting and collecting sensitive traffic without direct interaction with the end-user devices.
The strategic rationale behind targeting SOHO routers is profound. As Microsoft explained, "By compromising edge devices that are upstream of larger targets, threat actors can take advantage of less closely monitored or managed assets to pivot into enterprise environments." SOHO routers, often deployed in homes and small businesses, frequently lack the robust security configurations, regular patching, and continuous monitoring typically found in larger enterprise networks. They serve as a crucial gateway, and their compromise offers a stealthy vantage point for surveillance and potential further infiltration.
The scale of this campaign is significant, with Microsoft Threat Intelligence reporting that it has affected more than 200 organizations and over 5,000 consumer devices. The follow-on adversary-in-the-middle attacks have specifically targeted Transport Layer Security (TLS) connections to Microsoft Outlook on the web domains, suggesting a clear intent to harvest credentials and gain access to email communications. The impact has been felt across critical sectors, including government entities, IT organizations, telecommunications providers, and energy companies, highlighting a broad intelligence-gathering mandate aimed at strategic targets.
Forest Blizzard has a long and notorious history of state-sponsored cyber operations. Known for its persistent and sophisticated attacks, the group has been linked to numerous high-profile incidents, including the hacking of the Democratic National Committee in 2016, attacks against the World Anti-Doping Agency, and various campaigns targeting government and defense organizations globally. Their TTPs often involve spear-phishing, zero-day exploits, and sophisticated malware, all aimed at intelligence collection and strategic disruption. The current campaign against SOHO routers represents an evolution in their tactics, demonstrating a shift towards leveraging less-secured edge devices for pervasive, silent surveillance, which is harder to detect and remediate than direct endpoint compromises.

Implications for the Cybersecurity Landscape: A Dual Challenge
These two concurrent threats underscore the multifaceted and constantly evolving nature of the modern cyber threat landscape. The Storm-1175 Medusa ransomware campaign highlights the increasing speed and aggression of financially motivated cybercriminals. The shrinking dwell time – the period between initial compromise and detection or payload deployment – from months to mere days or even hours, places immense pressure on organizations to implement rapid detection and response capabilities. For sectors like healthcare and education, which are often resource-constrained, this rapid pace presents an existential challenge. Operational disruption, potential patient data breaches, and the severe financial burden of recovery can cripple vital services. The double-extortion model further compounds the risk, turning data theft into a powerful leverage tool, forcing organizations to consider not just system recovery but also the profound reputational and legal consequences of data exposure.
Conversely, Forest Blizzard’s router-based espionage campaign exemplifies the enduring threat posed by state-sponsored actors. Their focus on SOHO routers exposes a critical vulnerability in the digital ecosystem. Many individuals and small businesses may not prioritize the security of these devices, assuming they are low-risk or adequately protected by default. However, these routers serve as a crucial entry point and a potential blind spot for larger network compromises. The ability to intercept and manipulate traffic at this foundational level offers attackers unparalleled opportunities for intelligence gathering, potentially bypassing more robust perimeter defenses of targeted enterprises. This silent surveillance capability can persist for extended periods, providing a steady stream of sensitive information without triggering traditional security alerts. The targeting of government, IT, telecom, and energy sectors indicates a clear intent to gather strategic intelligence, monitor communications, and potentially lay groundwork for future disruptive operations.
Recommendations and Mitigation Strategies: Fortifying Defenses

Addressing these dual threats requires a comprehensive and multi-layered approach to cybersecurity.
For organizations facing the threat of fast-moving ransomware like Medusa, immediate and proactive measures are paramount:
- Vulnerability Management: Implement a rigorous patching schedule, prioritizing internet-facing systems and known exploited vulnerabilities. Utilize vulnerability scanners and penetration testing to identify and remediate weaknesses regularly.
- Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR): Deploy advanced EDR/XDR solutions across all endpoints and network segments to detect anomalous activity, rapid lateral movement, and the deployment of malicious tools.
- Network Segmentation: Isolate critical assets and sensitive data within segmented network zones. This limits the lateral movement of attackers and contains the impact of a breach.
- Multi-Factor Authentication (MFA): Enforce MFA for all user accounts, especially for administrative access and remote access services, to significantly reduce the risk of credential theft and abuse.
- Security Awareness Training: Educate employees about phishing, social engineering, and the importance of reporting suspicious activities.
- Backup and Recovery: Maintain immutable, offline backups of all critical data and regularly test recovery procedures to ensure business continuity in the event of a successful ransomware attack.
- Incident Response Plan: Develop and regularly rehearse a comprehensive incident response plan to ensure a swift and effective reaction to a ransomware event, minimizing downtime and data loss.
To counter sophisticated router-based espionage like that carried out by Forest Blizzard, specific attention must be paid to edge devices:
- Router Security: Users and administrators of SOHO routers must change default credentials immediately upon setup. Use strong, unique passwords for administrative interfaces and Wi-Fi networks.
- Firmware Updates: Keep router firmware updated to the latest version. Manufacturers frequently release patches for known vulnerabilities, and failure to update leaves devices exposed.
- Disable Unnecessary Services: Turn off features like remote management, Universal Plug and Play (UPnP), and guest Wi-Fi networks if they are not strictly necessary.
- Network Monitoring: Implement network monitoring solutions to detect unusual DNS requests, unexpected traffic redirection, or outbound connections from routers that should not be occurring.
- DNS Configuration: Verify that DNS settings on routers and end devices are pointing to trusted DNS servers. Consider using secure DNS services that offer additional protection against hijacking.
- Zero Trust Architecture: For larger organizations, adopting a Zero Trust security model, which assumes no implicit trust and verifies every access request, can help mitigate the risks of compromised edge devices.
- Threat Intelligence Integration: Integrate threat intelligence feeds, such as those provided by Microsoft Threat Intelligence, into security operations to identify indicators of compromise (IoCs) associated with known state-sponsored campaigns.
The combined warnings from Microsoft Threat Intelligence serve as a stark reminder of the persistent and evolving nature of cyber threats. From the rapid-fire financial extortion of ransomware groups to the patient, stealthy espionage of state-sponsored actors, organizations must confront a complex threat landscape. Proactive security measures, continuous monitoring, and a commitment to adapting defenses are no longer optional but are fundamental requirements for safeguarding digital assets and maintaining operational integrity in an increasingly interconnected and perilous world. The battle for digital security is continuous, demanding constant vigilance and collaboration across the cybersecurity community.