A new research report from Microsoft delivers a stark warning: no single technology can reliably distinguish AI-generated content from authentic media, and a deepening reliance on any one method risks misleading the public and eroding trust in digital information. The comprehensive study, titled "Media Integrity and Authentication: Status, Directions, and Futures," was produced under Microsoft’s Longer-term AI Safety in Engineering and Research (LASER) program and published late last month. Authored by a multidisciplinary team from across the company, led by Chief Scientific Officer Eric Horvitz, the report provides a critical evaluation of the three core technologies currently leveraged to authenticate digital media: cryptographically secured provenance, imperceptible watermarking, and soft-hash fingerprinting. Its central premise, as articulated within the document, is that "A priority in the world of rising quantities of AI-generated content must be certifying reality itself," underscoring the profound challenge posed by the proliferation of synthetic media.
The Imperfect Tools: Limitations of Current Authentication Methods
The Microsoft report meticulously dissects the inherent weaknesses and vulnerabilities present in each of the primary authentication methodologies when deployed in isolation. This detailed analysis reveals a landscape where even the most promising solutions are susceptible to manipulation or circumvention, highlighting the complexity of securing digital media integrity in the age of advanced generative AI.
Provenance Metadata: The Chain of Custody Under Threat
Provenance metadata, often considered the cornerstone of digital media authentication, is the most widely adopted approach. It functions by creating a secure, verifiable record of a piece of media’s origin and subsequent modifications, essentially a digital chain of custody. Much of its current implementation revolves around the Coalition for Content Provenance and Authenticity (C2PA) open standard, an industry-wide initiative that includes tech giants, media organizations, and academia, all working to develop technical standards for verifiable content provenance. C2PA aims to provide consumers with transparent information about the origin and history of media content, empowering them to make informed judgments about its trustworthiness. However, the Microsoft report identifies significant vulnerabilities: provenance data can be deliberately stripped away from content, forged outright, or undermined by local device implementations that lack robust cloud-level security controls. For instance, if a local camera or editing software is compromised, the provenance data it generates could be inaccurate or tampered with before it even enters a more secure system. This susceptibility means that while provenance offers a strong foundational layer, it cannot guarantee integrity if its initial capture or subsequent handling is insecure. The ease with which metadata can be altered or removed, even unintentionally during common sharing practices, further complicates its standalone reliability.
Imperceptible Watermarking: A Fragile Mark
Imperceptible watermarking involves embedding hidden information directly into the digital content itself, making it difficult for human perception to detect but readable by specialized software. These watermarks can carry data about the content’s origin, creation date, or even a unique identifier. While seemingly robust, the report cautions that watermarks, particularly those embedded on consumer-grade devices, can be removed through various digital signal processing techniques, compressed out during file conversions, or reverse-engineered by malicious actors. The ongoing "arms race" between watermarking techniques and removal algorithms means that any given watermark is unlikely to remain unassailable indefinitely. The very nature of "imperceptible" means that if the watermark can be detected by an algorithm, another algorithm can be trained to remove it, often with minimal impact on the content’s visual or auditory quality. This constant cat-and-mouse game renders watermarking a useful but ultimately insufficient defense on its own.
Soft-Hash Fingerprinting: The Challenge of Scale and Specificity
Soft-hash fingerprinting utilizes perceptual hashing, a technique that generates a unique "fingerprint" for a piece of media based on its visual or auditory characteristics, rather than its exact binary data. This allows for matching content even if it has undergone minor modifications, such as resizing, compression, or cropping, unlike cryptographic hashes which demand exact bit-for-bit matches. The system works by comparing these perceptual hashes against known databases of authentic or AI-generated content. While effective for identifying exact or near-exact duplicates, the report deems soft-hash fingerprinting unsuitable for high-confidence public validation. The primary reasons cited are the risk of hash collisions—where different pieces of content might generate similar fingerprints, leading to false positives—and the prohibitive costs associated with managing and constantly updating the enormous databases required to cover the vast and ever-growing volume of digital media. The dynamic nature of generative AI, which can produce endless variations, further exacerbates the challenge of maintaining a comprehensive and up-to-date database for detection. Furthermore, the inherent "softness" of perceptual hashes means they are designed to tolerate minor changes, which can be a double-edged sword when attempting to definitively label content as authentic or synthetic.
The Insidious Threat of "Reversal Attacks"
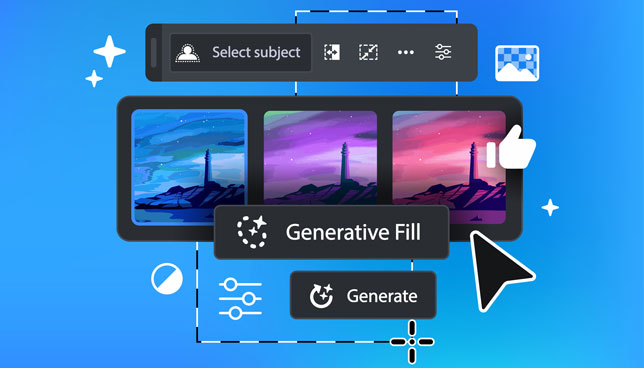
One of the report’s most alarming warnings centers on what researchers term "reversal attacks." These sophisticated attacks are designed to deliberately flip authentication signals, making genuine content appear to be AI-generated, and conversely, making AI-generated content appear authentic. The report outlines a chilling scenario: an attacker could take an entirely genuine photograph, apply a minor AI-assisted edit using a generative fill tool (e.g., to remove a small object or subtly alter a background), and then attach C2PA credentials that accurately disclose the AI involvement. While technically truthful about the minor modification, this disclosure could be strategically leveraged to cast widespread doubt on the authenticity of the entire original image, even though its core content remains genuine. Such an attack weaponizes transparency, turning a feature meant to build trust into a tool for disinformation. The psychological impact of these reversal attacks could be profound, systematically eroding public trust in all digital media, regardless of its true origin. If even demonstrably real content can be plausibly dismissed as AI-generated due to a minor, disclosed edit, the very concept of "truth" in digital media becomes deeply compromised, with far-reaching societal, political, and legal ramifications.

Towards a More Resilient Future: Recommendations and Combined Strategies
Given the individual limitations of current authentication methods, Microsoft’s research team advocates for a multifaceted, layered approach to securing media integrity. The report’s recommendations underscore the necessity of collaboration across the technology ecosystem, from content creators to distribution platforms and policymakers.
Synergistic Authentication: Provenance and Watermarking in Tandem
The most reliable approach, according to the researchers, involves combining provenance data with watermarking. This synergistic strategy creates a more robust defense than either method can offer alone. The report suggests that if a C2PA manifest is present and successfully validated—meaning its digital chain of custody is intact and verifiable—or if a detected watermark links back to a verified manifest in a secure registry, then the content can be treated with a high-confidence authentication. This dual-layer validation significantly raises the bar for attackers, requiring them to bypass or compromise two distinct and complementary security mechanisms. The C2PA standard itself is evolving to incorporate more robust mechanisms for linking content to its creator and modification history, making it a powerful partner to embedded watermarks. This combined approach also allows for redundancy; if one method is compromised, the other might still provide sufficient evidence of authenticity.
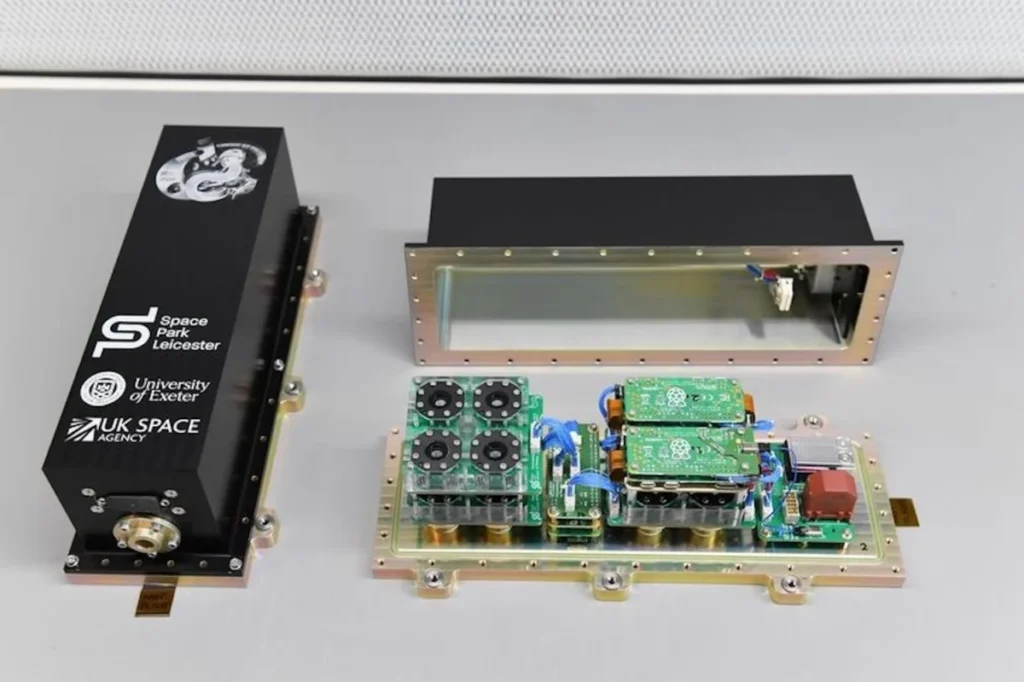
Hardware Security: Fortifying the Foundation
A critical concern highlighted in the report is the vulnerability of hardware. Local and offline systems, including most consumer cameras and PC-based signing tools, are inherently less secure than cloud-based implementations. The report explains that users with administrative control over a device may possess the ability to alter or bypass the tools that generate provenance data, thereby weakening the entire chain of trust at its source. For instance, a sophisticated attacker could modify firmware on a camera to generate false provenance data, making it appear as though an AI-generated image originated directly from a trusted device. To counter this, the report implicitly calls for hardware manufacturers to integrate more secure, tamper-resistant modules that can cryptographically sign content at the point of capture, making it much harder for local compromises to undermine the integrity of the initial provenance data. This would require a significant industry-wide shift towards secure-by-design principles for consumer electronics.

Calibrating Public Expectations and the Role of Education
The report emphasizes an urgent need for public education regarding the purpose and limitations of Media Integrity and Authentication (MIA) methods. Misconceptions and unrealistic expectations about the infallibility of detection tools can be just as damaging as the tools’ technical weaknesses. Before widespread policy adoption of these technologies, public expectations must be recalibrated to align with what these tools can actually deliver. This involves transparent communication from tech companies, media organizations, and educational institutions about the capabilities and limitations of AI detection and authentication technologies. Without a well-informed public, even the most advanced solutions risk being misunderstood, misused, or disbelieved, further contributing to the erosion of trust in digital media. Media literacy initiatives, explaining concepts like provenance, deepfakes, and the "cat-and-mouse" dynamic, are crucial to empowering individuals to critically evaluate the content they encounter online.
The Broader AI Detection Landscape: A Perpetual Arms Race
Beyond direct authentication, the report also addresses the efficacy of AI-based deepfake detectors—tools specifically designed to identify AI-generated content. While acknowledging their utility as a valuable last line of defense, Microsoft’s research team describes them as inherently unreliable. Proprietary detectors developed by Microsoft’s AI for Good team, for example, demonstrated accuracy in the range of 95% under non-adversarial conditions. However, the report strongly cautions that the "cat-and-mouse" dynamic between ever-improving AI generators and detection tools means no detection tool can be considered fully reliable. As generative AI models become more sophisticated, they will inevitably learn to evade existing detectors, necessitating constant updates and improvements in detection technology. This perpetual arms race implies that a definitive, static solution for AI detection is unlikely to emerge. The team further notes a critical psychological risk: high detector confidence may actually amplify the damage caused by false negatives. If a trusted detector confidently labels an AI-generated piece of disinformation as authentic, that result is far more likely to go unchallenged, potentially leading to widespread acceptance of false narratives. This underscores the danger of placing undue faith in any single AI detection system.
Microsoft’s Commitment to AI Safety and the Urgency of Provenance
These findings are not isolated but connect to a broader and deepening set of AI safety developments Microsoft has pursued in recent months. The company has proactively engaged in initiatives aimed at securing the AI ecosystem and fostering responsible development. In a significant move, Microsoft co-founded an open-source AI security initiative alongside industry leaders like Google, Nvidia, and others, signaling a collective commitment to addressing AI-related risks through collaborative research and shared standards. Furthermore, Microsoft has expanded its Security Copilot, integrating dedicated AI agents designed to automate threat detection and identity protection across complex enterprise environments, leveraging AI to combat AI-powered threats. In a separate analysis, the company had previously warned that generative AI is significantly accelerating the arms race between cyber attackers and defenders, necessitating a rapid evolution in cybersecurity strategies. This latest study on media integrity adds a new layer of urgency specifically around provenance infrastructure—the foundational technology that underpins how organizations, journalists, and consumers alike can verify what is real in an increasingly synthetic digital world. The report serves as a critical call to action, emphasizing that without robust and reliable provenance, the ability to discern truth from fabrication will become increasingly tenuous, threatening the very fabric of information exchange and public discourse.
A Collective Call to Action for the Digital Ecosystem
The Microsoft report concludes with a clear and actionable call to various stakeholders across the digital ecosystem, emphasizing that the challenge of media integrity is a shared responsibility requiring coordinated effort.

Generative AI Providers: The report urges creators of generative AI technologies to prioritize the integration of provenance and watermarking capabilities directly into their systems from the outset. This "security by design" approach would ensure that synthetic content is marked as such at its point of creation, rather than relying on retrospective detection. This includes embedding C2PA-compatible manifests and robust, perhaps even physically unclonable, watermarks within the generated output.
Distribution Platforms: Social media sites, news aggregators, and other distribution platforms are called upon to preserve C2PA manifest data throughout the upload, sharing, and display processes. Often, metadata can be stripped during compression or transcoding when content is uploaded to platforms. Ensuring that this crucial provenance data remains intact and accessible to users is vital for maintaining the chain of trust. This would require platform-wide technical standards and potentially new infrastructure to handle and display provenance information effectively.
Policymakers: The report advises policymakers to align legislative timelines and regulatory frameworks with what is technically feasible in the rapidly evolving field of AI authentication. Hasty or ill-informed regulations could stifle innovation or mandate solutions that are impractical or easily circumvented. Instead, policy should encourage research, foster industry collaboration, and support the development of open standards while acknowledging the inherent limitations of current technologies. This pragmatic approach would help avoid creating a false sense of security through legislation that cannot be effectively enforced or is quickly rendered obsolete by technological advancements.
The full report, a crucial resource for anyone concerned with the future of digital media and information integrity, is publicly available on the Microsoft Research website. Its findings serve as a potent reminder that while AI offers immense creative potential, it also presents unprecedented challenges to our collective ability to discern reality, necessitating a collaborative, nuanced, and continuously evolving approach to safeguard the authenticity of digital content.