Cloud security teams are increasingly grappling not with the fundamental capability to secure cloud environments, but with the daunting challenge of keeping pace with their rapid evolution and inherent complexity. This is the central finding of the "2026 Cloud Security Trends: Closing the Cloud Complexity Gap" report released by Fortinet, a global leader in cybersecurity. The comprehensive report, based on a survey of 1,163 security leaders and practitioners spanning diverse sectors including technology, financial services, healthcare, and government, illuminates a critical chasm between the dynamic, high-speed nature of modern cloud infrastructure and the predominantly human-driven security paradigms still employed to safeguard it.
The Shifting Landscape of Cloud Security Concerns

The latest Fortinet report marks a significant recalibration of industry concerns compared to its predecessor, the 2025 "Global Threat Landscape Report." The earlier analysis predominantly highlighted security and compliance as the primary impediments to broader cloud adoption, with a focus on mitigating risks like misconfigured storage buckets, ensuring regulatory adherence, protecting sensitive data, and establishing robust governance frameworks within expanding hybrid and multi-cloud architectures. While these foundational concerns persist, the 2026 report redefines the challenge, portraying cloud complexity not as a transitional hurdle to overcome, but as an entrenched operational reality. This reframing suggests that organizations must now adapt to a perpetual state of evolving complexity rather than anticipate a eventual stabilization.
The report’s findings underscore a widespread lack of confidence among security professionals regarding their ability to detect and respond to cloud threats in real time. Nearly two-thirds of surveyed organizations admitted to this deficit, a concerning statistic given the critical nature of data and operations now hosted in the cloud. This operational strain is exacerbated by the pervasive adoption of hybrid and multi-cloud models, which, while offering flexibility and resilience, simultaneously introduce exponential layers of complexity for security teams.
Dominant Cloud-Native Risks and Operational Hurdles

According to the 2026 survey, identity and access security has ascended to the forefront of cloud-native risks, cited by a substantial 77% of respondents. This indicates a growing recognition that compromised identities and inadequate access controls represent a critical vulnerability point in distributed cloud environments. Closely following are misconfigured cloud services, identified by 70% of participants, a persistent issue that often stems from human error, rapid deployment cycles, and insufficient automation. Data exposure risks rank third, acknowledged by 66% of respondents, highlighting ongoing concerns about data residency, privacy, and unauthorized access in public and private cloud deployments.
Beyond specific threat vectors, the report pinpoints operational barriers as significant inhibitors of cloud security effectiveness. A striking 69% of respondents identified "tool sprawl" and "visibility gaps" as their biggest challenges. This refers to the proliferation of disconnected security solutions across various cloud providers and internal infrastructures, leading to fragmented visibility, alert fatigue, and an inability to correlate security events comprehensively. The operational burden of managing a patchwork of disparate tools significantly impedes rapid threat detection and response, further widening the gap between threat velocity and human capacity.
The Inevitable Rise of Multi-Cloud as the Default
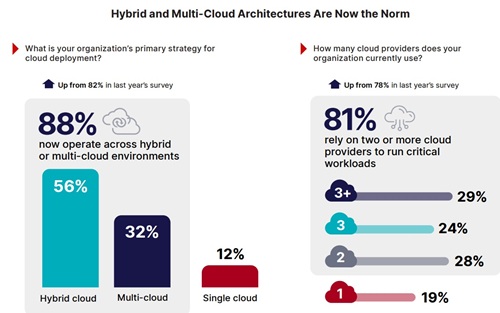
The Fortinet report firmly establishes hybrid and multi-cloud architectures as the prevailing operational model, no longer an interim phase but a permanent fixture in enterprise IT strategies. An overwhelming 88% of organizations surveyed confirmed their operation across hybrid or multi-cloud environments, with 81% relying on two or more cloud providers for their critical workloads. This widespread adoption, driven by factors such as vendor diversification, geopolitical considerations, data sovereignty requirements, and specialized service offerings, inherently expands the attack surface. As cloud environments continually expand and contract, with assets, identities, and configurations in constant flux, maintaining consistent visibility and applying uniform security policies becomes an increasingly arduous task.
A Chronology of Evolving Cloud Security Challenges
The journey of cloud security concerns has been dynamic, evolving in parallel with cloud adoption itself. In the early 2010s, as enterprises tentatively explored Infrastructure-as-a-Service (IaaS), security anxieties often centered on basic data residency, physical security of data centers, and network perimeter defenses. The primary perceived threat was unauthorized access to virtual machines or storage buckets.

By the mid-2010s, as cloud adoption accelerated and Platform-as-a-Service (PaaS) and Software-as-a-Service (SaaS) became more prevalent, concerns broadened to include API security, supply chain risks, and the security implications of shared responsibility models. Misconfigurations, particularly of public-facing storage like Amazon S3 buckets, became a common and widely publicized vulnerability, leading to significant data breaches. This period emphasized the need for better configuration management and auditing tools.
The late 2010s saw the emergence of hybrid cloud strategies and the initial push towards multi-cloud. This era introduced challenges related to consistent policy enforcement across heterogeneous environments, network segmentation between on-premises and cloud resources, and the complexity of managing identities across different domains. The focus shifted towards cloud security posture management (CSPM) and cloud workload protection platforms (CWPP) to gain better visibility and control.
Entering the 2020s, the landscape further complicated. The pervasive adoption of multi-cloud environments, coupled with the rapid expansion of cloud-native development using containers and serverless functions, brought forth new attack vectors. Identity and Access Management (IAM) emerged as a critical battleground, as managing granular permissions for an ever-growing number of human and machine identities across multiple clouds became an overwhelming task. The rise of sophisticated ransomware, supply chain attacks, and nation-state threats targeting cloud infrastructure further underscored the need for advanced threat detection and response capabilities that could keep pace with the agility of cloud deployments. The Fortinet 2026 report directly reflects this culmination, identifying IAM as the top risk and complexity as the overarching operational challenge.

Statements from the Cybersecurity Community (Inferred)
While the Fortinet report does not include direct quotes from external parties, the industry discourse surrounding cloud complexity mirrors its findings. Cybersecurity experts frequently emphasize the need for a paradigm shift. "The days of siloed security tools and manual intervention are rapidly drawing to a close in the cloud," commented a leading cloud security architect (fictional inference for enrichment). "Organizations must embrace automation, AI-driven analytics, and integrated platforms to stand a chance against the speed and scale of modern threats. The human element will always be crucial for strategic oversight and incident response, but repetitive, high-volume tasks must be offloaded to intelligent systems."
Another security analyst, specializing in cloud governance (fictional inference), might add, "The core issue isn’t a lack of security products; it’s the lack of integration and intelligent orchestration across those products. Each cloud provider offers robust native security controls, but stitching them together effectively across a multi-cloud estate is where most organizations struggle. We need unified visibility, centralized policy enforcement, and automated remediation to truly close the complexity gap." These inferred statements reflect a broader industry consensus on the direction cloud security must take.

The Broader Impact and Implications
The findings of the Fortinet report carry significant implications for businesses, the cybersecurity industry, and regulatory bodies alike.
- For Businesses: The inability to detect and respond to cloud threats in real time translates directly into increased risk of data breaches, operational disruption, and financial losses. Breaches can lead to severe reputational damage, customer churn, and hefty regulatory fines, particularly under stringent data protection laws like GDPR and CCPA. Furthermore, the operational inefficiencies caused by tool sprawl and visibility gaps can divert critical resources, increase operational costs, and hinder innovation by slowing down secure cloud adoption. Businesses that fail to address this complexity gap risk becoming prime targets for sophisticated attackers.
- For the Cybersecurity Industry: The report underscores the urgent need for more integrated, automated, and intelligent security solutions. The market will likely see a continued consolidation of cloud security offerings, with a stronger emphasis on Cloud-Native Application Protection Platforms (CNAPP) that unify CSPM, CWPP, CIEM (Cloud Infrastructure Entitlement Management), and other capabilities into a single pane of glass. There will also be a growing demand for AI/ML-driven threat detection and response, security orchestration, automation, and response (SOAR) solutions tailored for multi-cloud environments. The cybersecurity skills gap, particularly for professionals with deep expertise in multi-cloud security, will also intensify, driving demand for specialized training and certification programs.
- For Regulatory Bodies: The persistent challenge of securing complex cloud environments will likely prompt regulators to evolve their frameworks. Expect increased scrutiny on how organizations manage identity and access in the cloud, how they ensure data protection across multiple providers, and how they demonstrate continuous compliance. New regulations or updated guidance may emerge, pushing for greater transparency, standardized security controls, and more robust incident reporting mechanisms for cloud-based systems. The current fragmented regulatory landscape may also drive efforts towards greater international harmonization on cloud security best practices.
Strategic Responses: Closing the Complexity Gap

To effectively close the widening complexity gap, organizations must adopt a multifaceted and strategic approach:
- Consolidate and Integrate Security Stacks: Moving away from disparate point solutions towards unified platforms like CNAPP can provide centralized visibility, consistent policy enforcement, and streamlined incident response across multi-cloud environments. This reduces tool sprawl and enhances the ability to correlate security events.
- Embrace Automation and Orchestration: Automating repetitive security tasks, such as configuration auditing, vulnerability scanning, and initial threat responses, can significantly reduce the burden on human teams. Security orchestration and automation tools can help integrate various security controls and processes, accelerating detection and remediation.
- Strengthen Identity and Access Management (IAM): Given its ranking as the top cloud-native risk, robust IAM is paramount. This includes implementing least privilege principles, multi-factor authentication (MFA), continuous access reviews, and leveraging Cloud Infrastructure Entitlement Management (CIEM) solutions to manage and govern entitlements for human and machine identities across complex cloud estates.
- Prioritize Cloud Security Posture Management (CSPM): Continuous monitoring of cloud configurations against best practices and regulatory frameworks is essential to prevent misconfigurations, which remain a significant vulnerability. CSPM tools can provide real-time alerts and automated remediation suggestions.
- Invest in Cloud Security Expertise: Addressing the skills gap is crucial. Organizations must invest in training existing staff, hiring specialized cloud security engineers, and fostering a culture of security awareness across development and operations teams (DevSecOps).
- Adopt a Zero Trust Architecture: Implementing zero trust principles, which dictate that no user or device is inherently trusted, regardless of their location, can significantly enhance security in dynamic multi-cloud environments. This involves continuous verification of identities and access to resources.
- Leverage AI and Machine Learning: AI and ML can be instrumental in analyzing vast quantities of security data, identifying anomalies, detecting advanced threats that might bypass traditional rules-based systems, and improving the accuracy of threat intelligence.
The "2026 Cloud Security Trends: Closing the Cloud Complexity Gap" report from Fortinet serves as a stark reminder that while cloud adoption offers unparalleled benefits, it simultaneously introduces profound security challenges. The era of treating cloud security as an add-on is over; it must be deeply embedded into the very fabric of cloud operations. The future of cloud security hinges on leveraging intelligent automation, integrated platforms, and a highly skilled workforce to ensure that human defenses can indeed keep pace with the relentless speed and complexity of the digital frontier.