Across higher education, an undercurrent of unauthorized use of artificial intelligence is quietly shaping daily academic life, revealing critical institutional gaps rather than merely indicating misbehavior. This phenomenon, termed "shadow AI," manifests in various forms: faculty members leveraging generative AI tools like ChatGPT for drafting lesson plans and syllabi, researchers independently spinning up high-performance computing resources (GPUs) on public cloud platforms using personal or departmental credit cards, and students and staff inadvertently pasting sensitive institutional or personal data into consumer-grade AI tools without a full understanding of the inherent risks. These actions, far from being acts of rebellion, represent clear signals of unmet needs within the academic ecosystem, pointing to areas where official institutional support and infrastructure fall short of user demands.
The rapid proliferation and increasing accessibility of artificial intelligence tools, particularly generative AI models since late 2022, have created an unprecedented surge in their adoption across all sectors, including higher education. Users, driven by the promise of enhanced productivity, efficiency, and innovative problem-solving, are quick to integrate these powerful new capabilities into their workflows. When the officially sanctioned paths for AI adoption are either non-existent, cumbersome, or perceived as too slow, individuals inevitably seek alternative solutions. This instinct, honed over decades of navigating institutional bottlenecks and bureaucratic hurdles, leads them to "find a way," often outside official IT channels. For IT leaders in higher education, the fundamental task is not to implement stricter controls or punitive measures, but to listen attentively to what these workarounds are communicating about the institution’s current technological and support deficiencies.
The Historical Context: Lessons from Shadow IT
The concept of shadow AI is not entirely new; it echoes the long-standing challenges posed by "shadow IT." For decades, shadow IT has referred to the use of hardware or software within an enterprise without the explicit approval or knowledge of the IT department. This often involved departments purchasing their own software licenses, setting up local servers, or using unsanctioned cloud services to meet immediate operational needs that central IT was perceived as unable or unwilling to address quickly. Examples ranged from a marketing department using a consumer-grade project management tool to a research lab setting up its own data storage solution.
The motivations behind shadow IT are strikingly similar to those driving shadow AI: a perceived lack of agility from central IT, cumbersome procurement processes, a need for specialized tools not offered institution-wide, or simply a desire for greater autonomy and control. While shadow IT introduced risks related to security vulnerabilities, data silos, and compliance issues, shadow AI amplifies these concerns significantly due to the nature of AI technologies. AI systems frequently handle vast amounts of sensitive data, require intensive computational resources, and operate with complex algorithms that can have profound ethical and intellectual property implications. The lessons learned from managing shadow IT – that outright prohibition is often ineffective and that collaboration is key – are more pertinent than ever in the age of AI.

The Multifaceted Risks of Unsanctioned AI
While the immediate benefits of shadow AI to individual users can be compelling, the aggregated risks for an institution are considerably higher than those posed by traditional shadow IT. These risks span data privacy, cybersecurity, financial management, compliance, and intellectual property.
-
Data Privacy and Compliance Breaches: Many consumer AI platforms include terms of service that grant vendors broad rights to store, access, or even reuse user-generated data to train their models. If faculty, staff, or students input identifiable student information (protected by FERPA in the U.S.), sensitive patient data (HIPAA), proprietary research data, or other personally identifiable information (PII) into these tools, compliance with stringent privacy laws and grant requirements can unravel instantly. A single instance of a student pasting an essay containing personal details into a public AI chatbot could constitute a FERPA violation. Similarly, researchers working on human subjects research must adhere to strict confidentiality protocols; an uncontrolled AI service capturing even a fragment of a dataset could erode trust, jeopardize ethical approvals, and lead to severe institutional penalties. International regulations like GDPR further complicate matters, imposing strict rules on cross-border data transfer and processing.
-
Cybersecurity Vulnerabilities: Shadow AI tools, by their very nature, operate outside the institution’s established security perimeter. They may lack the necessary security controls, regular patching, and monitoring that central IT applies to approved systems. This creates new entry points for cyberattacks, making the institution more susceptible to data breaches, ransomware, and intellectual property theft. Malicious actors could potentially exploit vulnerabilities in unsanctioned AI applications to gain access to broader institutional networks, or use AI-generated content (e.g., phishing emails, deepfakes) as part of social engineering attacks.
-
Financial Inefficiencies and Resource Drain: The uncoordinated adoption of AI tools leads to a chaotic financial landscape. Departments or individual researchers might purchase redundant licenses for similar AI services, or incur unpredictable and often exorbitant bills for cloud-based GPU usage. This fragmented spending prevents the institution from leveraging economies of scale, negotiating favorable enterprise-wide contracts, or optimizing resource allocation. Moreover, a patchwork of disparate AI systems becomes exponentially harder – and more expensive – to integrate, manage, and secure over time. AI also demands thoughtful data pipelines and sustainable compute planning. When departments "go it alone," campuses lose the ability to align AI growth with shared infrastructure, sustainability goals, and overarching security standards, leading to an inefficient ecosystem built by improvisation, riddled with blind spots.
-
Intellectual Property and Research Integrity: For a research-intensive university, intellectual property (IP) is a cornerstone of its mission. Researchers rely on strict confidentiality until their work is published or patented. If an unsanctioned AI tool captures research data, algorithms, or unique methodologies, it could compromise the novelty of discoveries, jeopardize patent applications, and potentially transfer ownership rights to third-party AI vendors, undermining the institution’s competitive edge and future funding opportunities. Furthermore, the ethical implications of AI use in academic work, such as undisclosed AI assistance in student assignments or research papers, can erode academic integrity and trust.
-
Operational Silos and Lack of Strategic Alignment: When AI adoption occurs in isolated pockets, the institution loses the ability to develop a cohesive AI strategy. This leads to redundant efforts, missed opportunities for collaboration, and a fragmented approach to leveraging AI for institutional benefit. It becomes challenging to standardize best practices, share knowledge, or ensure that AI initiatives align with the university’s broader strategic goals, such as enhancing learning outcomes, streamlining administrative processes, or fostering groundbreaking research.
From Restriction to Response: A Strategic Shift
Faced with these significant risks, many CIOs and university administrators initially gravitate towards familiar instincts: more controls, stricter gates, and mandatory training sessions. However, experience with shadow IT has demonstrated that tighter rules rarely eradicate unsanctioned activity; instead, they often drive it further underground, making it harder to detect and manage. This approach also misses the fundamental point: shadow AI is not merely a compliance issue; it is a critical feedback mechanism. Every instance of shadow AI points directly to the friction users feel, the clarity they lack, and the gaps between what they need and what the institution currently provides.
The institutions making real progress in navigating the AI landscape are not attempting to eradicate shadow AI through prohibition. Instead, they are learning from it, treating it as valuable intelligence. They are replacing roadblocks with guardrails, aiming to build systems and pathways that make the sanctioned and secure option the easiest and most attractive one for users. This strategic shift requires a multi-pronged approach focused on understanding user needs, providing robust alternatives, and establishing clear, supportive governance.

A Playbook for Turning Shadow AI into Strength
Successfully transforming shadow AI from a threat into a strategic asset involves several key components:
-
Discovery and Assessment: The first step is to understand the scope and nature of shadow AI. This involves proactive engagement with faculty, researchers, and students through surveys, interviews, and focus groups. IT departments need to ask: What AI tools are people currently using? Why are they using them? What problems are they trying to solve? What are their pain points with existing institutional resources? This empathetic discovery phase helps uncover hidden needs and provides crucial insights into potential solutions.
-
Communication and Education: Clear, consistent, and practical communication is paramount. Institutions must educate their community not just about the risks of unsanctioned AI, but also about the approved tools and services available. This education should be tailored to different user groups (e.g., researchers, instructors, students) and focus on practical implications, such as what constitutes sensitive data, how to identify appropriate AI tools, and the ethical considerations of AI use. Providing clear guidelines on acceptable use, data handling, and academic integrity is essential.
-
Provisioning and Enablement: This is arguably the most critical component. Institutions must proactively provide user-friendly, secure, and performant AI tools and resources that meet the community’s needs. This could involve:

- Enterprise AI Platforms: Licensing enterprise-grade generative AI tools with robust data privacy agreements.
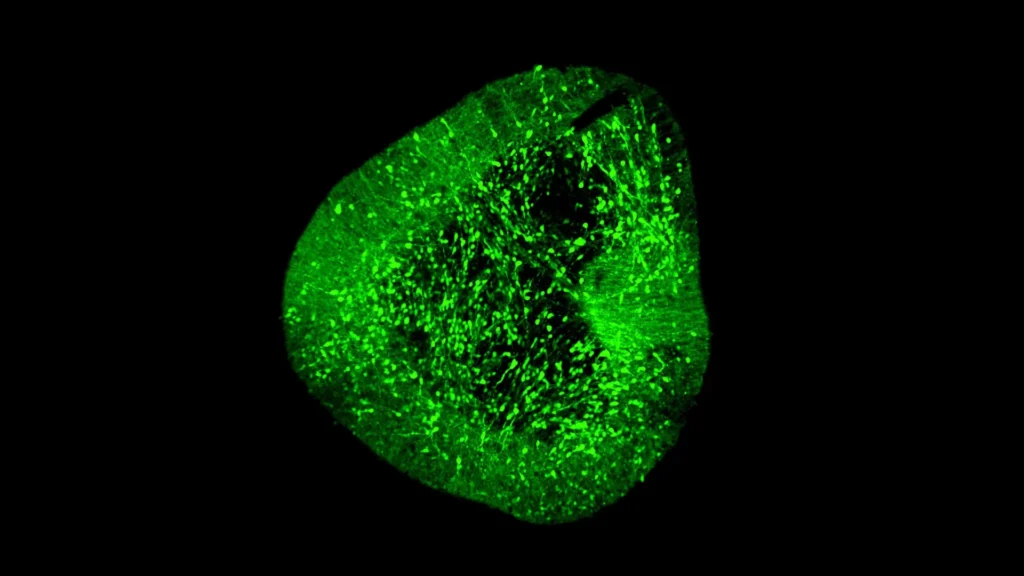
- Secure Research Environments: Offering managed cloud environments or on-premise high-performance computing resources specifically designed for AI workloads, complete with integrated data storage, security controls, and compliance frameworks.
- Specialized AI Services: Providing access to niche AI tools or APIs that cater to specific academic disciplines.
- AI Development Sandboxes: Creating secure "sandboxes" where researchers and students can experiment with AI models and develop custom applications without exposing sensitive data.
- User Support and Consultation: Offering expert consultation services to help users identify appropriate AI solutions, understand best practices, and navigate technical challenges.
-
Governance and Policy Frameworks: While avoiding overly restrictive rules, institutions must establish clear, adaptable governance frameworks. This includes developing policies around acceptable AI use, data privacy, intellectual property, ethical guidelines for AI development and deployment, and procedures for evaluating and onboarding new AI technologies. These policies should be developed collaboratively with stakeholders from academic departments, legal, research ethics, and student affairs.
-
Continuous Adaptation and Iteration: The AI landscape is evolving at an unprecedented pace. Institutions must adopt a mindset of continuous learning and adaptation. This means regularly reviewing AI policies, assessing new technologies, gathering feedback from users, and iterating on provided solutions. An agile approach ensures that the institution’s AI strategy remains relevant and responsive to the community’s evolving needs.
Case Study: Washington University in St. Louis
Washington University in St. Louis exemplifies this proactive and user-centric approach. Its research IT team has shifted away from a reactive, gatekeeping mentality towards an enabling one. Instead of presenting new faculty with a labyrinthine maze of storage tiers, compute options, and data requirements, they onboard researchers with essential resources and environments ready on day one. This includes pre-configured, secure cloud environments with access to necessary computational resources and data storage solutions, all compliant with institutional policies and grant requirements.
By designing environments for both speed and safety, the university significantly reduces the temptation for researchers to "swipe a credit card" for unofficial cloud resources. This approach not only enhances security and compliance but also accelerates research outcomes by removing initial friction points. The IT team acts as a partner, providing guidance and infrastructure that allows researchers to focus on their work, confident that their data is secure and their methods are compliant. This model illustrates that by making the sanctioned path the easiest and most efficient one, institutions can naturally guide users towards secure and compliant AI adoption.

Broader Impact and Future Implications
The challenge of shadow AI extends beyond immediate risk mitigation; it represents a pivotal moment for higher education IT. It forces institutions to rethink their role, moving from mere technology providers to strategic enablers of innovation. Embracing shadow AI as a signal necessitates a fundamental cultural shift within IT departments – from a focus on control to one of collaboration, empathy, and service excellence.
In the long term, effectively addressing shadow AI will enable universities to:
- Foster Innovation: By providing secure and accessible AI tools, institutions can empower faculty and students to explore new research avenues, develop innovative teaching methodologies, and enhance learning experiences.
- Strengthen Research Competitiveness: Centralized, well-managed AI infrastructure can provide a competitive advantage, attracting top researchers and enabling groundbreaking discoveries while protecting intellectual property.
- Improve Operational Efficiency: Strategic AI adoption can streamline administrative processes, optimize resource allocation, and enhance data-driven decision-making across the institution.
- Cultivate Digital Fluency: By offering sanctioned AI tools and comprehensive training, universities can better prepare students and faculty for an AI-driven future, embedding digital literacy and ethical AI use into the academic fabric.
Ultimately, shadow AI is not merely a problem to be solved, but a catalyst for necessary institutional evolution. By listening to the signals it sends, higher education institutions can transform potential threats into opportunities for innovation, efficiency, and sustained academic excellence in an increasingly AI-powered world. The future of higher education hinges on its ability to embrace and strategically manage these powerful new technologies, ensuring they serve the academic mission responsibly and effectively.