The popular Canvas learning management system, a cornerstone of digital education for millions of students and educators worldwide, has been hit by a second significant cybersecurity incident within a mere eight days. The latest breach, occurring on May 7th, follows an earlier attack on April 29th, raising serious concerns about the security of student data within educational technology platforms. Instructure, the company behind Canvas, confirmed the incidents and acknowledged that threat actors exploited vulnerabilities within its Free-For-Teacher accounts to gain unauthorized access. As a direct consequence, Instructure has announced the temporary shutdown of these accounts, a critical component of the Canvas ecosystem, to mitigate further risks.
This series of attacks underscores a growing vulnerability within the ed-tech sector, where vast amounts of sensitive personal and academic information are stored. Canvas, utilized by countless K-12 institutions and higher education establishments, houses student records including grades, assignment submissions, attendance data, and course materials. The implications of such breaches are far-reaching, potentially impacting the privacy and academic continuity of hundreds of millions of users.
A Timeline of Disruption and Data Exposure
The first reported incident occurred on April 29th, where Instructure confirmed that specific personal information of Canvas users at affected organizations was exposed. This data included names, email addresses, student identification numbers, and internal messages exchanged within the platform. The company’s initial public announcement, made via a website status update, aimed to inform users and stakeholders about the breach.
Just over a week later, on May 7th, a second, distinct cybersecurity incident took place. While Instructure stated that no additional data was accessed during this subsequent breach, the unauthorized actor did make changes to the pages that users encountered upon logging into Canvas. This manipulation could have led to misleading information, phishing attempts, or further disruption of the learning environment.
The proximity of these two attacks, occurring within an eight-day span, has amplified concerns among educational institutions and cybersecurity experts. The exploitation of Free-For-Teacher accounts suggests a targeted approach by threat actors seeking to leverage a specific, perhaps overlooked, vulnerability within the platform’s infrastructure.
The ShinyHunters Connection and Wider Reach
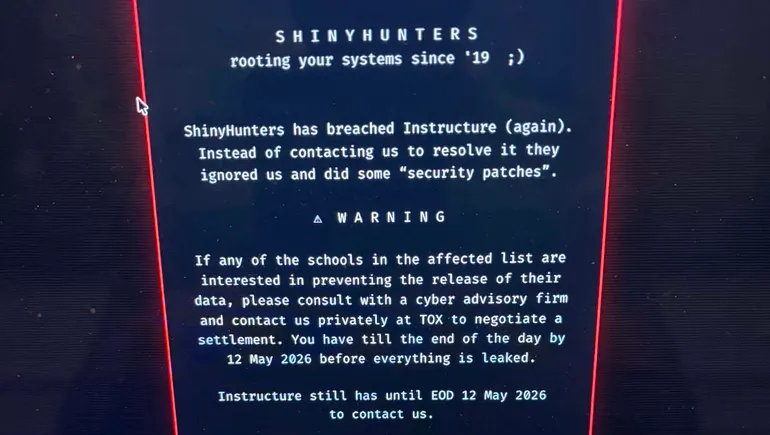
Evidence suggests a connection between these Canvas breaches and a known cybercrime group called ShinyHunters. According to The Daily Pennsylvanian, the University of Pennsylvania’s independent student newspaper, Canvas users at the institution encountered a message originating from this group. This message linked to a list of schools allegedly impacted by ShinyHunters’ data breaches into Canvas.
The message further indicated that affected schools could negotiate a settlement with the cybercrime group by a specific deadline, May 12th. Notably, this deadline was the same one presented to Instructure, suggesting a coordinated or at least contemporaneous effort by the threat actors. Reports from student publications at other prominent universities, including Harvard University, the University of Oklahoma, and various University of California campuses, indicated similar messages appearing on their Canvas systems, pointing to a widespread, albeit potentially localized, impact.
The existence of such messages, linking to lists of affected schools and offering negotiation terms, is a common tactic employed by ransomware and data extortion groups. It highlights the sophisticated nature of these attacks and their potential to disrupt not just individual institutions but entire educational networks.
Institutional Responses and User Alerts
Educational institutions that utilize Canvas have been proactive in communicating with their student and staff populations. Roanoke County Public Schools in Virginia issued a statement acknowledging the May 7th incident, informing their users that they "may have seen a message today related to this incident on their computers when they logged into the Canvas system." The district’s advisory urged students and staff to refrain from engaging with any such messages, a standard precaution in the face of potential phishing or malware attempts.
The fact that users at multiple universities encountered direct messages from the alleged cybercrime group suggests a significant level of intrusion. The messages served as a stark reminder of the ongoing threat landscape and the immediate impact such incidents can have on daily academic life.
Expert Analysis: The Criticality of Data Protection
The Canvas incidents have drawn sharp criticism and raised urgent calls for improved cybersecurity practices within the ed-tech sector. Elizabeth Laird, director of equity in civic technology at the nonprofit Center for Democracy & Technology, emphasized the tangible consequences of failing to secure sensitive student and teacher data. In a statement on May 8th, Laird highlighted that the incident not only disrupted essential learning activities but also exposed personal information of "nearly 300 million users," including potentially sensitive messages.
Laird further pointed to broader systemic issues that exacerbate these vulnerabilities. She cited the recent closure of the U.S. Department of Education’s Office of Educational Technology, an office that previously assisted schools with responsible technology use, and significant funding cuts to cybersecurity support for educational institutions. "This is an important wakeup call," Laird stated, "that schools and the companies that work with them have legal and ethical responsibilities to safeguard students and teachers online in the same ways that they are protected in the classroom."
Shaila Rana, a cybersecurity professor at Purdue Global and a senior member of the Institute of Electrical and Electronics Engineers, echoed these concerns. In a May 8th statement to K-12 Dive, Rana underscored the limited control students and staff have over their data within ed-tech platforms. She described an "asymmetry" where users cannot opt out, meaningfully audit data protection practices, or avoid consequences when breaches occur. Rana also highlighted the critical infrastructure dependency of platforms like Canvas, noting that its disruption during finals week simultaneously impacted academic continuity across thousands of institutions.
Kate Brody, policy director at Schools Beyond Screens, an organization advocating for reduced technology reliance in schools, saw the Canvas incident as a prime example of why educational institutions need to "interrogate their overuse of technology." This perspective suggests a need for a fundamental re-evaluation of the digital tools adopted by schools and the inherent risks associated with centralizing vast amounts of sensitive data.
A Pattern of Ed-Tech Vulnerabilities
The Canvas breaches are not isolated events in the landscape of educational technology. The ed-tech sector has seen a series of high-profile cyberattacks in recent years, indicating a persistent challenge in securing student data. Notable previous incidents include:
- PowerSchool: A cloud-based K-12 software provider that experienced a significant data breach. Investigations and legal proceedings following this incident have highlighted lessons learned regarding data security in school management systems.
- Illuminate Education: A student information system provider that reached a settlement with the Federal Trade Commission (FTC) over its 2021 data breach, which exposed sensitive information of millions of students.
These recurring incidents paint a concerning picture of the cybersecurity posture within the ed-tech industry. The reliance on third-party vendors to manage student data creates a complex chain of responsibility, where a single vulnerability in one platform can have widespread repercussions.
The Broader Implications for Education
The Canvas cybersecurity incidents serve as a critical reminder of the multifaceted challenges facing modern education. As schools increasingly integrate digital tools to enhance learning, the protection of student data must be paramount. The implications extend beyond immediate data exposure:
- Erosion of Trust: Repeated breaches can erode the trust that students, parents, and educators place in educational institutions and the technology they employ.
- Academic Disruption: As demonstrated by the timing of the Canvas breaches during potentially critical academic periods, disruptions can have a direct impact on student progress and institutional operations.
- Regulatory Scrutiny: Increased incidents are likely to lead to greater regulatory scrutiny and potentially stricter compliance requirements for ed-tech companies and school districts.
- Cost of Remediation: Recovering from a data breach involves significant costs, including forensic investigations, system security enhancements, legal fees, and potential settlements or fines.
- Privacy Rights: The exposure of student data, particularly personal messages and academic records, raises profound privacy concerns and potential for misuse.
The temporary shutdown of Canvas Free-For-Teacher accounts, while a necessary step, also highlights the potential impact on educators who rely on these tools for their classrooms. Finding a balance between robust security measures and the continued availability of essential educational resources remains a critical challenge.
In conclusion, the repeated cybersecurity incidents targeting the Canvas learning management system by Instructure are a significant wake-up call for the entire ed-tech ecosystem. They underscore the urgent need for enhanced security protocols, greater transparency, and a more robust commitment to safeguarding the sensitive data of students and educators in an increasingly digital educational landscape. The industry, along with educational institutions, must proactively address these vulnerabilities to ensure that technology serves as a secure and reliable foundation for learning.