CHICAGO – In an era where digital infrastructure is as critical to education as textbooks and classrooms, small K-12 school districts face a disproportionate threat from cyber incidents. Limited budgets and lean technical teams often leave these institutions vulnerable to data breaches, ransomware attacks, and service disruptions caused by both malicious actors and natural disasters. However, a pragmatic, five-point model, bolstered by a wealth of free and shared resources, offers a pathway to enhanced cyber resilience, as detailed by three leading K-12 technology experts at the Consortium for School Networking’s (CoSN) annual conference on April 15, 2026.
The conference, a premier event for K-12 technology leaders, convened in Chicago to address the evolving challenges and opportunities in educational technology. This year’s sessions highlighted the increasing need for robust cybersecurity strategies, particularly for districts operating with constrained financial and human resources. Ed McKaveney, technology director at Hampton Township School District in Pennsylvania; Richard Platts, chief technology officer of Allegheny Intermediate Unit in Pennsylvania; and Chris Smallen, chief technology officer of Lenoir City Schools in Tennessee, presented their actionable framework designed to empower these smaller districts.
"Disruptions come in many forms," McKaveney shared with attendees, recounting a significant weather event from the previous spring. "Last spring, we had a huge storm come through. It wasn’t a tornado, but it was, like, multiple tornado paths just throughout the whole county. We ended up having no power for however many days, plus no internet for the rest of the week after we had power restored." This anecdote underscored that cyber readiness extends beyond digital threats to encompass broader resilience against unforeseen events that can cripple essential educational services.
The presenters emphasized that regardless of the specific nature of a disruption or the size of a school district, proactive steps can be taken to achieve a state of cyber readiness. Their recommended five-point model aims to provide a foundational structure for districts to build upon, ensuring essential cybersecurity basics are consistently addressed.

The Five-Point Model for K-12 Cyber Readiness
While the specific details of all five points were not fully enumerated in the session’s overview, the core tenets revolved around proactive planning, resourcefulness, collaboration, and continuous improvement. The presenters stressed that effective cybersecurity is not a one-time fix but an ongoing process that requires strategic investment of time and effort, even when financial capital is scarce.
A significant portion of the presentation focused on the critical strategy of leveraging available resources, particularly those that are free or can be shared among districts. This approach acknowledges the budgetary realities faced by many smaller school systems.
Maximizing Free and Shared Resources
"Resources are available to help fill gaps for tech leaders in districts with limited budgets," the presenters collectively stated, highlighting the importance of looking beyond internal capabilities for support.
Consortium for School Networking (CoSN) Resources:
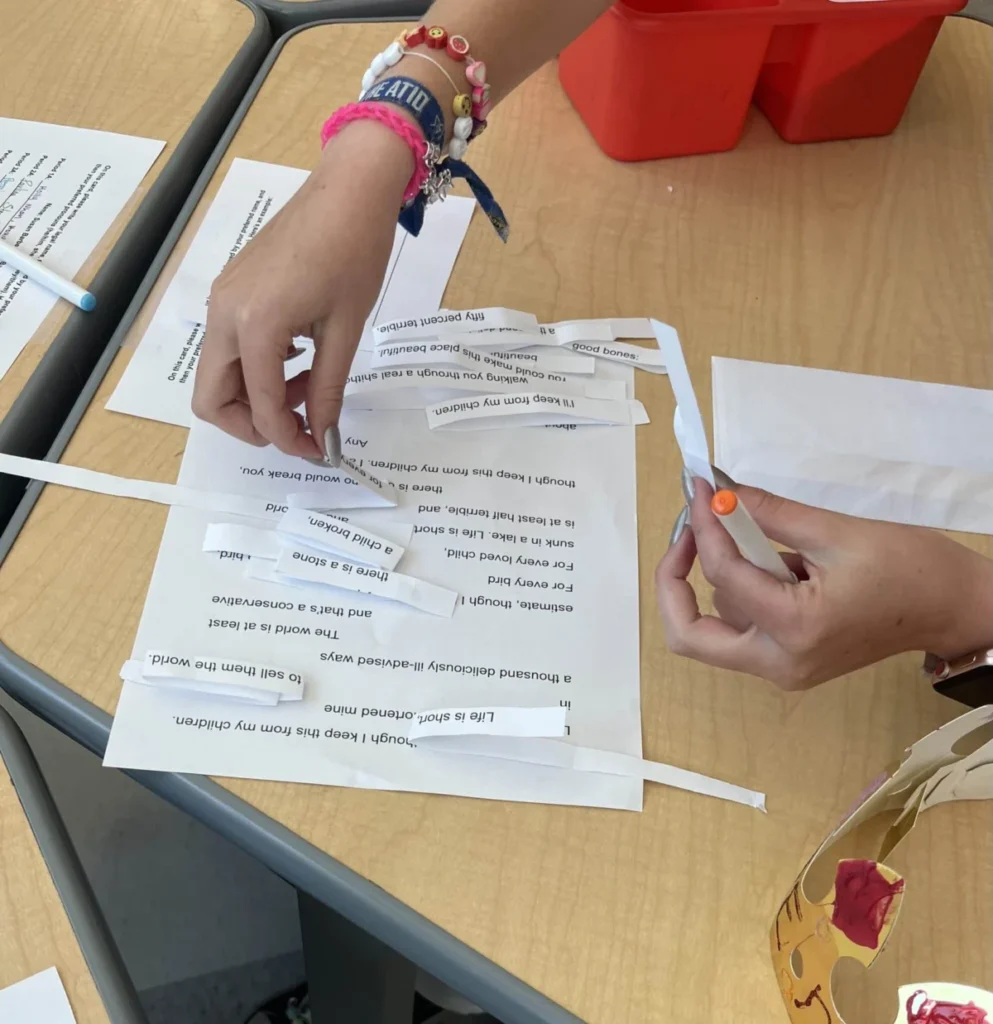
CoSN, the organizing body of the conference, offers a robust suite of resources specifically tailored for K-12 technology leaders. These include:
- One-Pagers: These concise documents are designed to be easily digestible and serve as valuable "conversation starters" when communicating technology needs, particularly cybersecurity requirements, to superintendents and school boards. They can help translate technical concerns into understandable terms, facilitating better decision-making and resource allocation.
- Best Practice Guides: CoSN provides in-depth guides and frameworks covering various aspects of educational technology, including cybersecurity policies, incident response planning, and data privacy.
- Webinars and Professional Development: Access to expert-led webinars and online training sessions offers continuous learning opportunities for tech staff, keeping them abreast of the latest threats and mitigation strategies without significant travel costs.
- Networking Opportunities: CoSN events and online forums foster a community where technology leaders can share challenges, solutions, and best practices, creating a valuable peer-support network.
McKaveney noted that CoSN’s one-pagers are particularly useful for articulating needs. "They can be ‘conversation starters’ when communicating needs to superintendents," he explained. This practical application of CoSN’s materials can be instrumental in securing buy-in for essential cybersecurity investments.

U.S. Cybersecurity and Infrastructure Security Agency (CISA) Toolkit:
Another crucial resource highlighted was the U.S. Cybersecurity and Infrastructure Security Agency’s (CISA) "Protecting Our Future: Cybersecurity K-12" toolkit. This comprehensive resource provides actionable guidance, best practices, and tools specifically developed for K-12 organizations. The toolkit addresses a wide range of cybersecurity topics, from basic cyber hygiene to more advanced threat mitigation and incident response. Its availability as a free public resource makes it an indispensable asset for districts seeking to enhance their security posture without incurring licensing fees.
Building Relationships with Law Enforcement:
The presenters strongly advocated for proactive engagement with law enforcement agencies, particularly the FBI. McKaveney emphasized the importance of establishing a relationship before an incident occurs. "The first time that you’ve made contact with your FBI liaison shouldn’t be the first time you end up having an issue. Just at least know the person and have their phone number," he advised.
Platts lightheartedly commented on the necessity of such connections: "I never imagined I would have multiple FBI special agents’ cell phone numbers in my contacts." McKaveney acknowledged the unusual nature of these relationships, noting, "It is a little weird-feeling sometimes." However, this proactive outreach can significantly expedite response times and provide invaluable support during a cyber crisis, leveraging specialized expertise that districts often lack internally. The presence of dedicated FBI field offices across the country offers a geographically accessible point of contact for many districts.
Partnerships with Higher Education:
Colleges and universities were also identified as potential allies for resource sharing and knowledge exchange. McKaveney pointed out that many small private universities share similar operational scales and challenges with school districts. "A lot of school districts are bigger than a lot of the small colleges and universities," he said. "Some small private universities are the same size as your school districts. You have the same challenges, just different funding strategies and things like that."
These institutions can offer expertise in areas such as cybersecurity research, student interns who can assist with IT tasks, or even shared access to specialized software or training platforms. Developing these academic partnerships can create a symbiotic relationship where both entities benefit from shared knowledge and resources, helping to bridge the gap in technical capabilities for smaller districts.

The Broader Implications for K-12 Cybersecurity
The challenges faced by small school districts in cybersecurity are symptomatic of a larger trend: the increasing reliance on digital systems in education coupled with persistent underfunding in critical infrastructure. According to recent reports, the average cost of a data breach in the education sector has continued to rise, with ransomware attacks becoming particularly prevalent. A 2025 report by a cybersecurity firm indicated that K-12 institutions were among the most targeted sectors for ransomware, with average recovery costs exceeding $1 million, a figure often prohibitive for smaller districts.
The vulnerability of student and staff data is a paramount concern. Personal identifiable information (PII), including social security numbers, addresses, and medical records, is highly valuable to cybercriminals. A breach can lead to identity theft, financial fraud, and significant reputational damage for the school district. Furthermore, disruptions to educational technology can impede learning, impacting student achievement and the continuity of essential services.
The five-point model and the emphasis on resourcefulness presented at the CoSN conference offer a strategic blueprint for mitigating these risks. By adopting a proactive stance, embracing collaboration, and leveraging existing free and shared resources, even the smallest districts can build a more robust and resilient cybersecurity posture. This approach not only protects sensitive data but also ensures that the educational mission can continue uninterrupted, regardless of external threats or unforeseen circumstances.
The presenters’ insights underscore a critical message: effective cybersecurity is not solely dependent on budget size, but on strategic planning, informed decision-making, and the willingness to collaborate and innovate within the available ecosystem of support. As technology continues to integrate deeply into the fabric of education, the principles championed at CoSN’26 will be essential for safeguarding the future of learning for all students.